Celo validator roundup, October 2020
October was a quiet month for the Celo netowrk. Not much has changed since our last September update, but we will still review all the numbers once again.
Overview

Voter rewards target APY continues to decrease slowly. While amount of Locked CELO hasn’t changed significantly, the overall percentage of Locked CELO remains high enough that target APY will continue to decrease.
Below we can look at two interesting graphs. First one shows total locked CELO, and second one shows CELO that is held in release gold contracts and is not yet liquid. The daily step ladder increases come from epoch rewards. Sharp drops in RGLocked graph shows more CELO becoming liquid and available to withdraw from existing ReleaseGold contracts.

We can see that even though there are times when CELO gets unlocked (presumably to be sold on the open market), whoever ends up acquiring that CELO, tends to lock it up again anyways.
Attestations
We will look at the same stats as we did in our last release to track progress of Celo adoption.


The numbers for daily registered addresses/users remains the same. There hasn’t been any significant increase in traction overall. Averaging <20 new registered addresses daily, with a larger spike in first week of this month.
Not much improvement is seen with overall attestation deliveries either. The graph below shows percentage of unique users that have failed to complete even a single attestation, aggregated over a 24h time period. (See our September release for more details on this stat).

Core contracts upgrade
As mentioned in our last issue, there is an on-going effort to perform first core contracts upgrade on the Celo network: https://forum.celo.org/t/governance-proposals-to-make-the-protocol-safe-and-easy-to-upgrade/615
Upgrade process ran into a minor issue due to misconfigured Governance proposal: https://forum.celo.org/t/rejecting-cgp-11-increase-gaslimit-to-13m/645. This issue has now been resolved and upgrade process is back on track to be completed sometime in November.
Per-block Gas limit has now increased to 13 million up from 10 million in Mainnet, which should now allow for core contracts upgrade transaction to safely proceed. Note that 13 million gas limit is still too small for currently deployed slashing contract to work, thus slashing is still not available until the upgrade is completed.
Validator Performance
October was more or less standard as far as overall validator uptime goes. There were 2 groups that crossed the slash-able threshold this month. Validators should become increasingly aware that after November, slashing will most likely be fixed and penalties for slash-able downtime will be enforced. This will lead to very large drops in offending validator group rewards, thus it is important to make sure all the operational practices are in-place now, to avoid any further extended downtimes.
Two groups that crossed the slash-able threshold were:
ThePassiveTrust (ThePassiveTrust-V1 validator)
BitCandy (DarkChocolate validator)
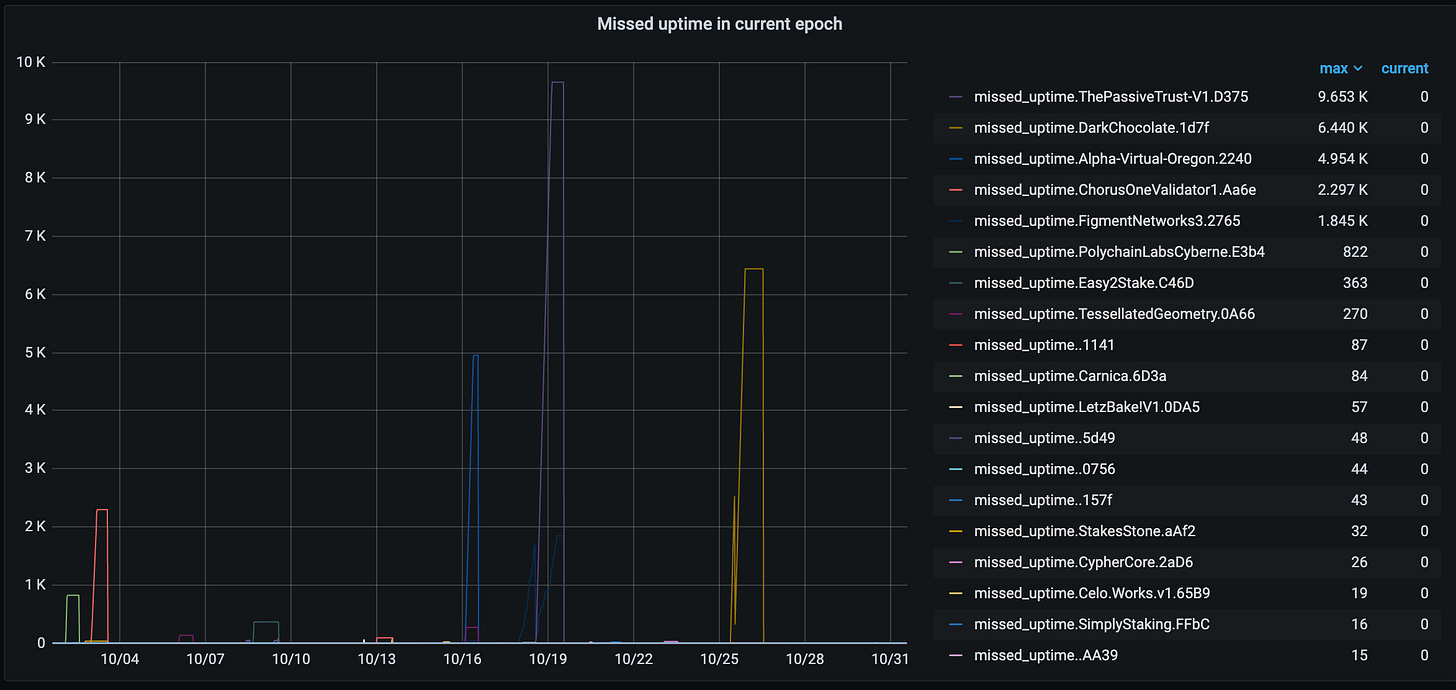
Few groups had some minor issues (or just minor downtime due to restarts).

And even fewer groups had larger outages. Notice that Alpha Virtual group cumulatively had almost as much downtime as The Passive Trust group, but they never crossed the slash-able threshold. This is an important difference because without slashing, the difference for voter rewards is almost negligible between any two groups. But with slashing enabled, the slashing penalty will add significant difference with the rewards.

If you are curious to see full performance/uptime stats for validator groups since Genesis (and not just for month of October), you can always check them here: https://celovote.com/scores. It is great to see that there are still quite a lot of groups that have had perfect or close to perfect uptime, running for >6months now.
Looking forward…
There seems to be some stagnation with the Valora app adoption and attestation progress overall, but hopefully next wave of projects and efforts picks it back up starting in November.
For validators, there are multiple important upgrades to watch out for:
Eventual hard-fork at the end of the year (or maybe start of 2021 if things get delayed).
Once core contracts upgrade enables slashing, extended downtime will become significantly more expensive for validator groups. Now would be a good time to make sure that all the operational practices are in-place to handle these upgrades without any significant downtime.

